Cybersecurity education: Tackling the compliance burden with a GRC program
The field of Governance, Risk, and Compliance (GRC) grew out of tools and practices designed to help organizations assess and mitigate the risks associated with their operations. We now associate GRC primarily with the tools and platforms used to run the various parts of the GRC program, but what are the essential elements needed to understand risk, develop governance, and ensure compliance?
Compliance is frequently the driver of a GRC implementation, so if you aren’t sure where to get started, we recommend our webinar The Compliance Conundrum. As you’ll see below, compliance is a natural starting point for building out a GRC program. It can be helpful for organizations that are growing quickly and need a leg up on assessing and mitigating risk.
Gimme a G, R, C!
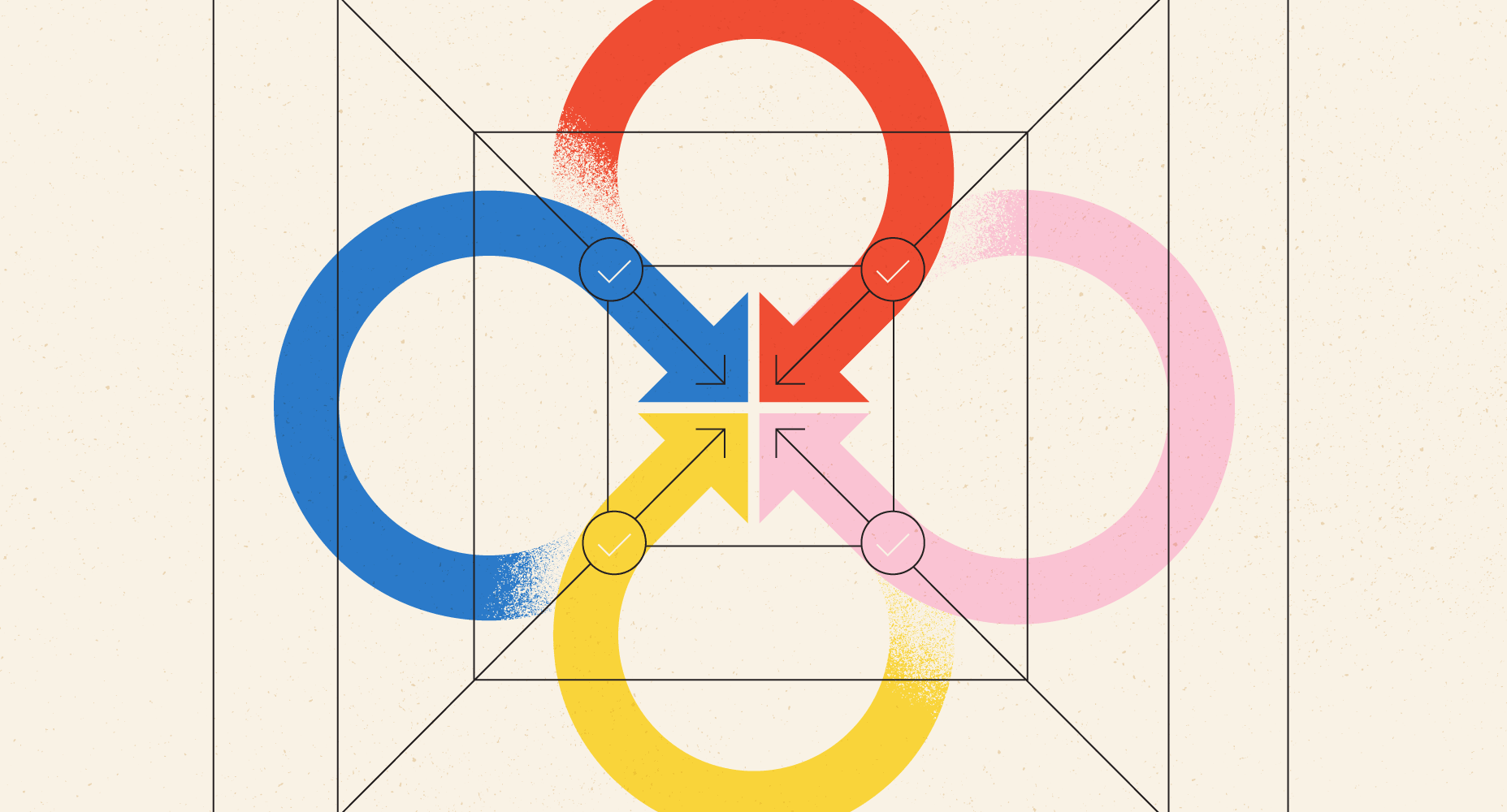
GRC is a hybrid of several practice areas and tools — the term was popularized in a market research study highlighting the convergence of different tools and processes under an umbrella goal of managing risk. Therefore, it’s helpful to break down each of the practice areas to understand how they differ and how they mutually support each other:
Governance is the guidelines or rules put in place to regulate (govern) how the organization operates. These may be aligned with customer requirements like protecting data to build trust, internal objectives like manufacturing sustainability, or even investors who want to see a company provide positive returns. Management and leadership are most often the sources of governance, and security policies are the most common forms of cybersecurity governance.
Risk (often Risk Management) is the practice of identifying, assessing, and taking steps to mitigate or treat risks. Risk is any possible future action that could occur — both positive and negative — but risk management usually focuses on adverse risks that could disrupt operations, such as a system outage, data breach, or cyber crime.
Compliance means following rules set out by somebody, often in the form of government or regulators. The Payment Card Industry Data Security Standard (PCI DSS) is one example, and it’s propagated by the PCI council to reduce payment card fraud. Compliance involves implementing controls aligned with the rules, operating them to achieve the desired outcome, and monitoring the status of the controls (both internally and often via external audits).
Risk management underpins all aspects of GRC. Writing policies and other documentation to govern organizational operations can prevent unwanted activities and ensure processes are executed in accordance with requirements, and that governance is the way management addresses the risks identified during a risk assessment. Identifying and assessing risks is fundamental to designing controls, such as choosing multi-factor authentication (MFA) and data encryption to protect systems and data from unauthorized access.
Compliance activities fit into the picture in one of two ways: firstly, audits and oversight ensure that governance is being followed and controls are working as intended. Secondly, external compliance frameworks can allow an organization to jumpstart their GRC program by providing pre-bundled risk identification and control suggestions. For example, PCI DSS deals with common risks to payment card data and lays out 12 required controls to mitigate them. Organizations that do not currently have a cybersecurity program can use compliance frameworks to get a head start, but with one important caveat: no one-size-fits-all approach will work. The compliance framework is a starting point and should be tailored to your organization’s unique needs.
Grand unified theory, or how a GRC tool centralizes work
There is a large amount of work to be done in a GRC program. For example, risk assessment and management are ongoing processes, audits and oversight should follow a continuous monitoring approach, and the design and implementation of security controls should be adaptable to support business agility. Centralizing those tasks into a unified toolset offers the advantage of reducing overhead and increasing shared resources across different teams. Some examples of GRC tool benefits include:
Leveraging work across multiple compliance frameworks: Many businesses face the burden of complying with multiple sets of rules, such as ISO 27001 and SOC 2. A GRC tool can help identify the compliance objectives you’re trying to meet, and then let you map controls that meet multiple objectives. For example, access controls like a password policy are fundamental in most compliance frameworks, and a GRC tool can let you see how that one policy checks boxes across ISO 27001, PCI DSS, and SOC 2.
Continuous oversight: Integrations are a common feature in GRC tools. They provide visibility into the status of technical controls; common examples include integrations with cloud hosting environments to monitor server configurations or pulling in data from security tools like endpoint detection and response (EDR) to identify malware incidents. Many GRC tools include task assignment and tracking, allowing you to track the status of routine processes such as manual access control reviews or physical facility security walkthroughs.
Dashboards and orchestration: Management loves metrics, and it’s doubly important for many GRC activities because they are usually a cost center rather than a revenue generator. Showing the effectiveness of your risk management efforts and communicating the value they deliver to the business is critical, so the dashboards and data in a GRC tool are invaluable. These dashboards can also be useful to practitioners responsible for scheduling and executing the tasks associated with a GRC program, showing the status of activities like control implementation or routine tasks like annual policy refreshes.
Not all organizations will need a dedicated tool to manage governance, risk, and compliance. Small businesses, such as those with <250 employees, or businesses in non-regulated industries (i.e., without a significant regulatory compliance burden) can often get by with some basic security policies in a shared drive and a single document for risk assessment and control documentation. Managing risk is all about cost-benefit analysis, so if your organization doesn’t need the capabilities of a GRC tool, then the cost is likely not justifiable. However, keep in mind that your GRC program will also need to scale as your business grows, so it’s crucial to monitor the business and identify the point when DIY tools become more of a headache than cost savings.
Partner spotlight: get a handle on compliance with Reciprocity
While audits typically have a negative connotation, Coalition policyholders can now remove the guesswork regarding governance, risk, and compliance (GRC). Reciprocity simplifies audit and compliance management with complete views of information environments, easy access to program evaluation, and continual compliance monitoring. With Reciprocity’s ZenGRC, policyholders can easily leverage their audit, third-party risk solutions, and policy management applications. Remaining compliant with industry standards and global requirements translates to lower risk and dollars saved.
Reciprocity’s mission is to turn corporate compliance from a cost center into a valuable strategic asset. ZenGRC provides one platform for all your organization’s audit, risk, third-party risk solutions, and governance and policy management applications.
Coalition Policyholders get exclusive savings from Reciprocity and can sign up for their services in Coalition Control, our active risk management platform with free, integrated attack surface monitoring.
Additionally, Coalition’s cybersecurity guide outlines the basic tenets of a cybersecurity program — a critical factor in reducing your organization’s cyber risk.








