Your insurance
wasn’t built for a digital world
In fact it was created to manage the risk of ships at sea almost 400 years ago.
Here’s the problem:
Digital technology allows us to move faster than ever before.
About 100,000,000 times faster than those ships.
Every minute on the planet there are:
208,000
people on Zoom
500,000
hours of YouTube uploaded
1,000,000
ecommerce transactions
208M
emails sent
Our hyper-connected digital world has created a new class of digital risk
Digital risks are evolving as quickly as our technology, often hiding in plain sight as the flow of information accelerates and threatens the things we value most.

It’s time for a new approach
One that can keep pace with the digital economy and do more than simply transfer risk, it can help you solve it.


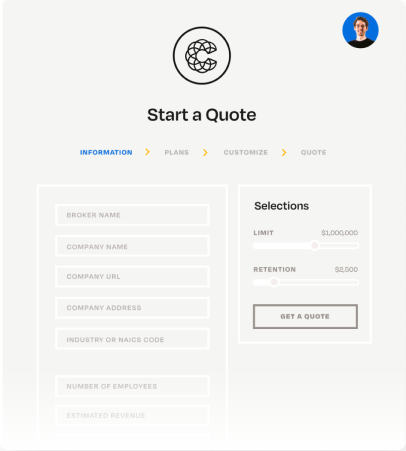
Protection Designed for digital risk
Digital risk is fast moving, unpredictable, and can be catastrophic for any organization. Protect your clients’ most valuable assets with an insurer who has the tech and insurance expertise to be a long term partner in the digital economy.


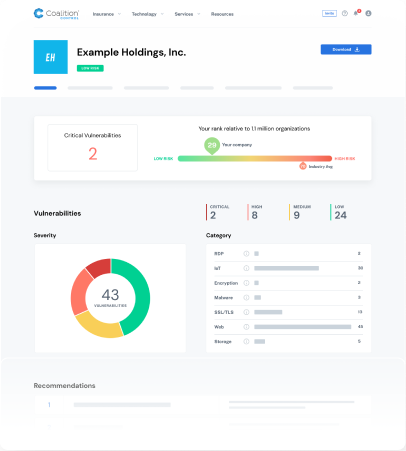
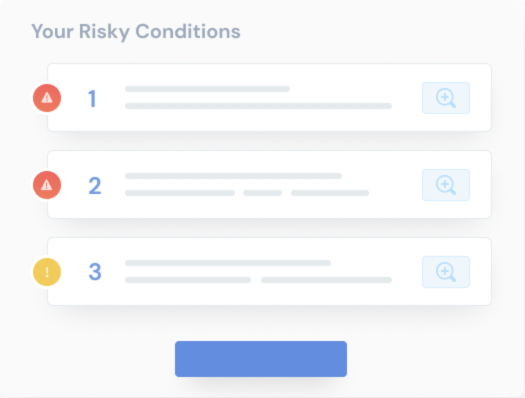
Prevent Risk Before it Strikes
Our personalized risk profile identifies the risks that are relevant to an organization, provides ongoing monitoring and protection from emerging vulnerabilities, and includes preventative measures to limit exposures before an attack