Data & Insights

Blog
5 Essential Insights From Our 2026 Cyber Claims Report
Discover how Active Insurance is helping businesses overcome the Cyber Protection Paradox with insights from Coalition’s 2026 Cyber Claims Report.

Blog
Powered by the Active Data Graph
Coalition’s Active Data Graph unearths the cyber threats that are most likely to result in losses and distills that data into actionable insights.

Blog
The State of Active Insurance: 2024 Cyber Claims Report
Discover the latest trends in ransomware, funds transfer fraud, risky technology, and the state of Active Insurance in Coalition’s 2024 Cyber Claims Report.
Blog
The Double-Edged Sword of Using Boundary Devices
Boundary devices can help mitigate cyber threats and enable secure remote access. However, these technologies are often directly targeted in cyber attacks.

Blog
LockBit Ransomware Used in Exploitation of ConnectWise ScreenConnect
Coalition Incident Response has discovered a link between the LockBit ransomware gang and the ConnectWise ScreenConnect vulnerabilities.
Blog
Cyber Threat Index 2024: Scans, Honeypots, and CVEs
The Coalition Cyber Threat Index uses our data derived from internet scans, honeypots, and vulnerabilities to provide in-depth cyber insights for 2024.
Blog
From Widespread Damage to Failure to Launch: The Celebrity CVEs of 2023
The number of CVEs has been steadily rising for years. Coalition reflects on the CVEs from 2023 that were the most (and least) impactful.

Blog
How Broker Roles Evolve Alongside Claims Trends
Businesses are getting hit harder and more often with cyber attacks — and they’re increasingly turning to their trusted brokers for guidance.

Blog
Preserving Data Privacy in a Digital Age
Organizations that fail to prioritize data privacy can put themselves at risk not only of the direct impacts of a cyber attack but also liability to others.
Blog
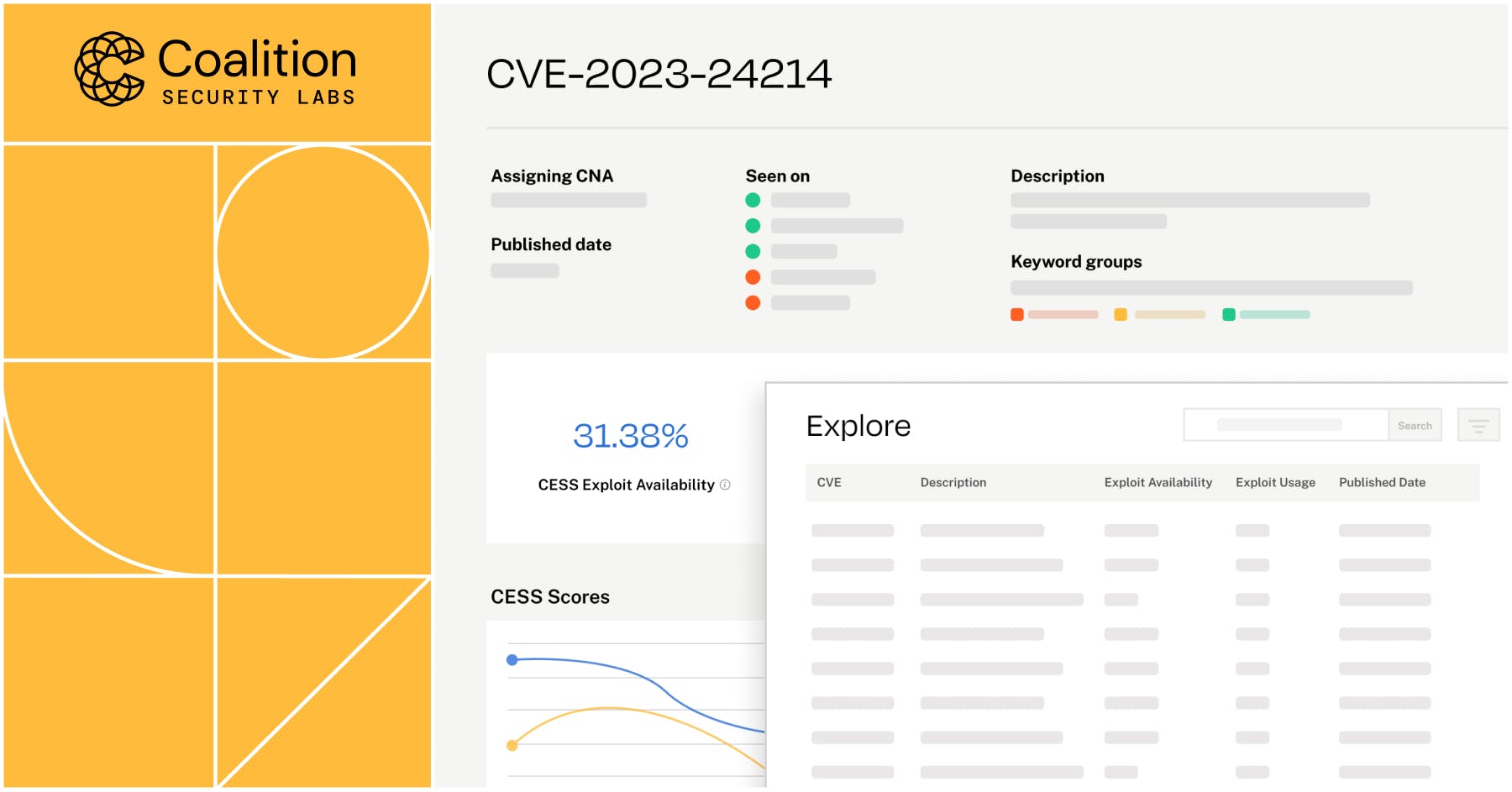
Announcing Coalition Exploit Scoring System (ESS)
Coalition Exploit Scoring System (ESS) helps defenders cut through the noise of vulnerability management. Learn how our dynamic scores work and try the tool.
Blog
The Art (and Peril) of Modeling Catastrophic Cyber Risk
Coalition dives deeper into cyber catastrophe models and explains what makes our approach to cyber risk aggregation unique.

Blog
How Coalition Recovered $5.5M After Funds Transfer Fraud
After a Coalition policyholder mistakenly wired money to a fraudulent account, our claims team jumped into action and recovered 85% of the initial loss.

Blog
Announcing Control 2.0: Coalition’s Cyber Risk Management Platform
Coalition Control 2.0 is now live for all users, featuring enhanced attack surface monitoring capabilities and improvements to the user interface.

Blog
Announcing Coalition Security Labs
Announcing Coalition Security Labs, our research and innovation center providing insights to help face the ever-evolving cyber threat landscape.