New Claims Report sees sharp increase in funds transfer fraud attacks

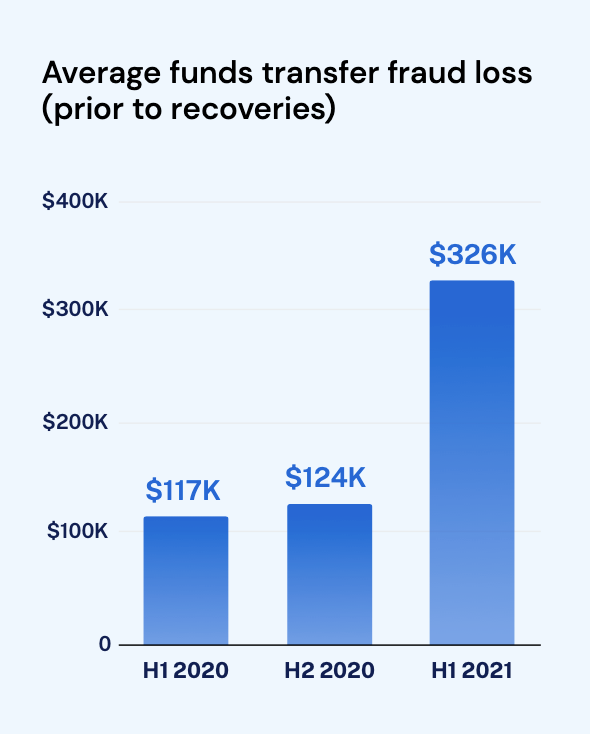
Funds transfer fraud (FTF), one of the easiest ways for attackers to monetize cyber crime against your organization, increased in frequency and severity over the last year. The associated losses surged threefold from H1 2020 to H1 2021. While ransomware requires sophisticated attack techniques and specialized malware, it is possible to execute an FTF attack without triggering any security alerts. Our H1 2021 Cyber Insurance Claims Report analyzed claims data through June 2021 from customers in the United States and Canada and found that funds transfer fraud is now the second most common incident type, increasing by 28%. The average loss before clawing back funds also surged in H1 2021 to a painful $326,264.
Ransomware and funds transfer fraud account for 50% of all known losses.
Our visibility into cyber incidents comes from three primary sources: our policyholders reporting incidents and claims, data the National Association of Insurance Commissioners (NAIC) shares with us, and finally, from the tens of thousands of insurance applications we receive each year. This is our second year compiling data to assess trends in cyber insurance.
An attack that can cripple your organization
Throughout 2020, many companies shifted to remote work. This moved most (if not all) of their operations online, forcing more communication to take place via email. Unfortunately, the rushed transition resulted in many organizations overlooking security risks, failing to recognize that the technologies that allowed their employees to work from home efficiently also gave attackers prolonged access to their critical systems and information. Criminals seized these new opportunities, opting to target new industries and smaller businesses, crafting more sophisticated social engineering scams. Imagine the email subject line: “Due to COVID-19, we are changing our payment procedures.”
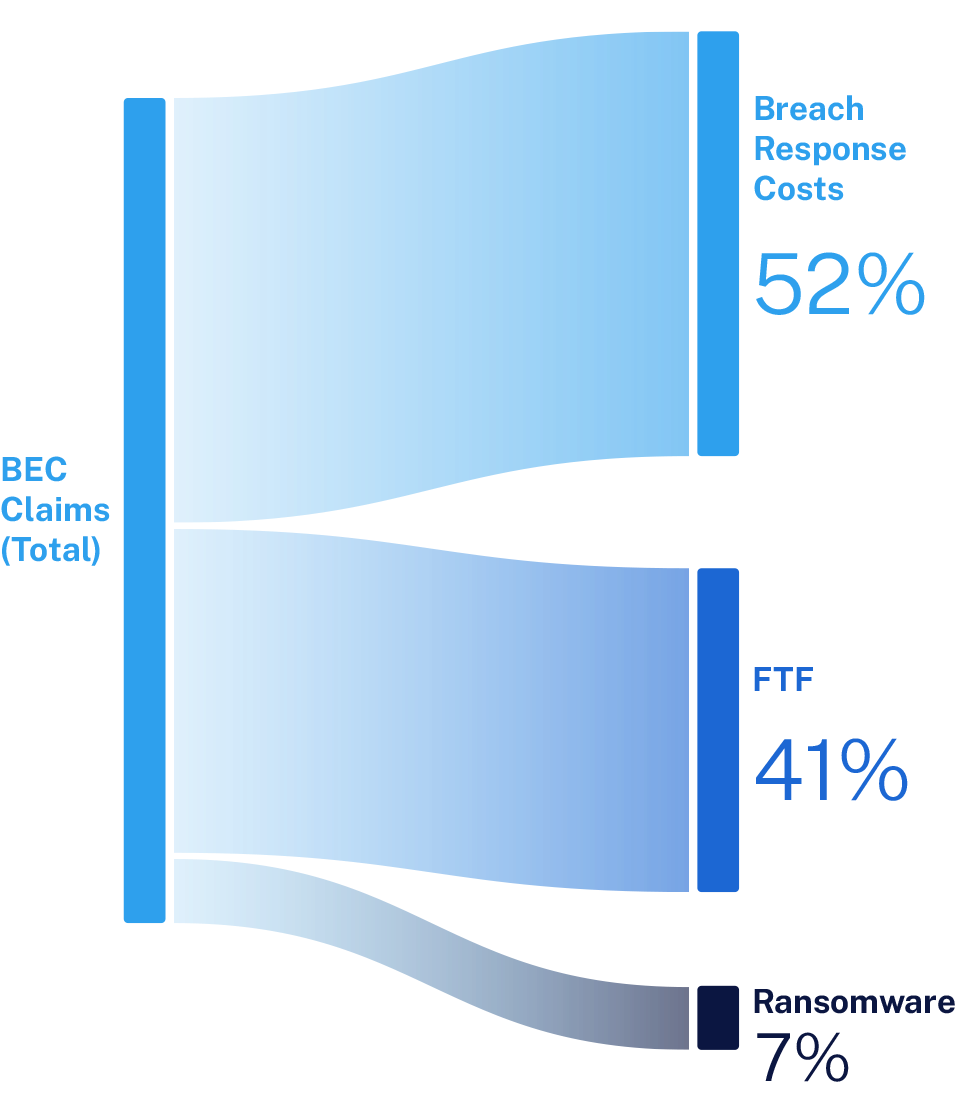
The average amount of funds stolen increased 179% from the first half of 2020 to 2021, from $116,842 to $326,264. Generally, a funds transfer fraud event begins with a phishing email or typical business email compromise (BEC), followed by social engineering. A BEC can lead to a wide array of losses — in 2020, 41% of BEC attacks evolved into an FTF incident resulting in the direct loss of funds. Attackers identify their victims, steal their credentials, and log in to their accounts, where they employ several different tactics to gain access to funds.
Once an attacker has access to an email inbox, they can search for transactions to intercept, hide valid emails using mailbox rules, modify payment instructions requests, or manipulate contacts to make fraudulent payments. They will send spoofed emails, fake invoices, and even make phone calls to appear legitimate and convince their target to wire funds. Once the attacker has accessed the funds, they will repeat this pattern on other contacts of the compromised mailbox user.
Download the full H1 2021 Cyber Insurance Claims report here to learn more about these trends and our predictions for the remainder of 2021.
How to recover — speed is essential
Funds transfer fraud losses can be devastating for any business, but there are steps your organization can take in the event of a fraudulent transfer. We recommend policyholders take immediate action to maximize their chances of recovery.
Notify Coalition’s claims team of the loss as soon as possible, ideally within 72 hours of the transfer.
Immediately notify your bank of the fraudulent transfer, and request a clawback of the funds.
File a report with the FBI at IC3.gov.
File a report with your local police department.
Repeatedly inquire with your bank and the receiving bank on the status of the recovery.
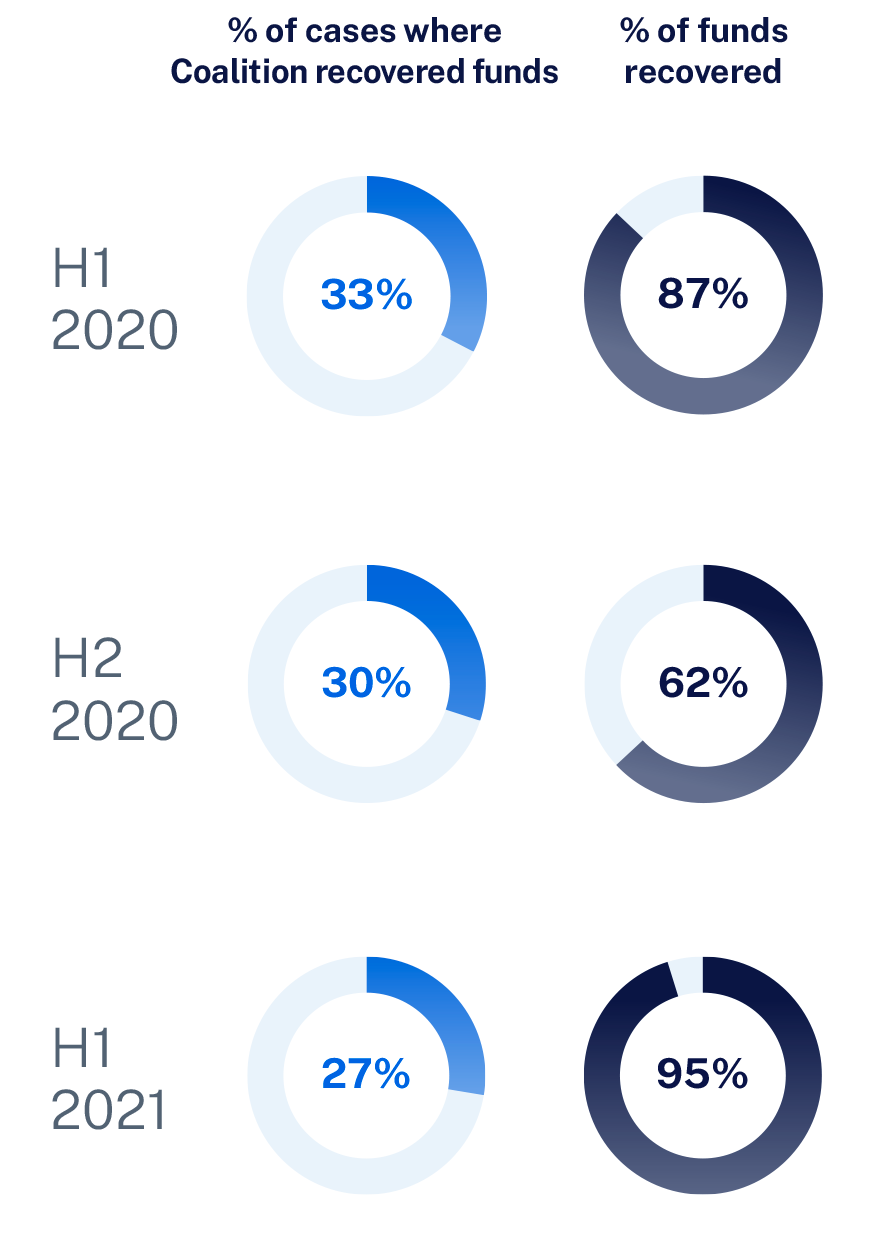
While the frequency of FTF cases is increasing, Coalition’s Claims and Incident Responses teams have successfully clawed back funds. We recovered 95% of funds in H1 2020, an increase from 87% in the first half of 2020. Once a policyholder notifies us a transfer has occurred, these teams will spring into action, working to cancel transactions and claw back funds before the attackers can withdraw them.
How to protect your organization
The primary defense against funds transfer fraud is a defined process for how your organization processes new requests and change payment requests. The procedures should include calling the requesting party on a known good number to confirm the demand — never use the contact information provided in an email as these are often manipulated during BEC incidents. These verification procedures should also have a defined, two-party approval process for transfers and required reviews for payment change details.
Many things have evolved since our last report. We see smaller organizations (250 employees or under) being targeted, and attackers are growing stealthier. But one thing remains consistent — attackers look for targets of opportunity that have made poor technological choices. Coalition Control, our risk monitoring platform, can assist with making good decisions to address and mitigate your cyber risk. Coalition Control includes free attack surface monitoring for everyone and provides ongoing scanning, monitoring, and alerting to all users.







