Announcing Coalition Exploit Scoring System (ESS)
Cybersecurity defenders have a difficult job. Thousands of new vulnerabilities are released each month, and managing scarce security resources is already hard when you have a new critical vulnerability. It becomes even harder when scoring is delayed, making the level of actual risk unclear and prioritization a more complicated challenge.
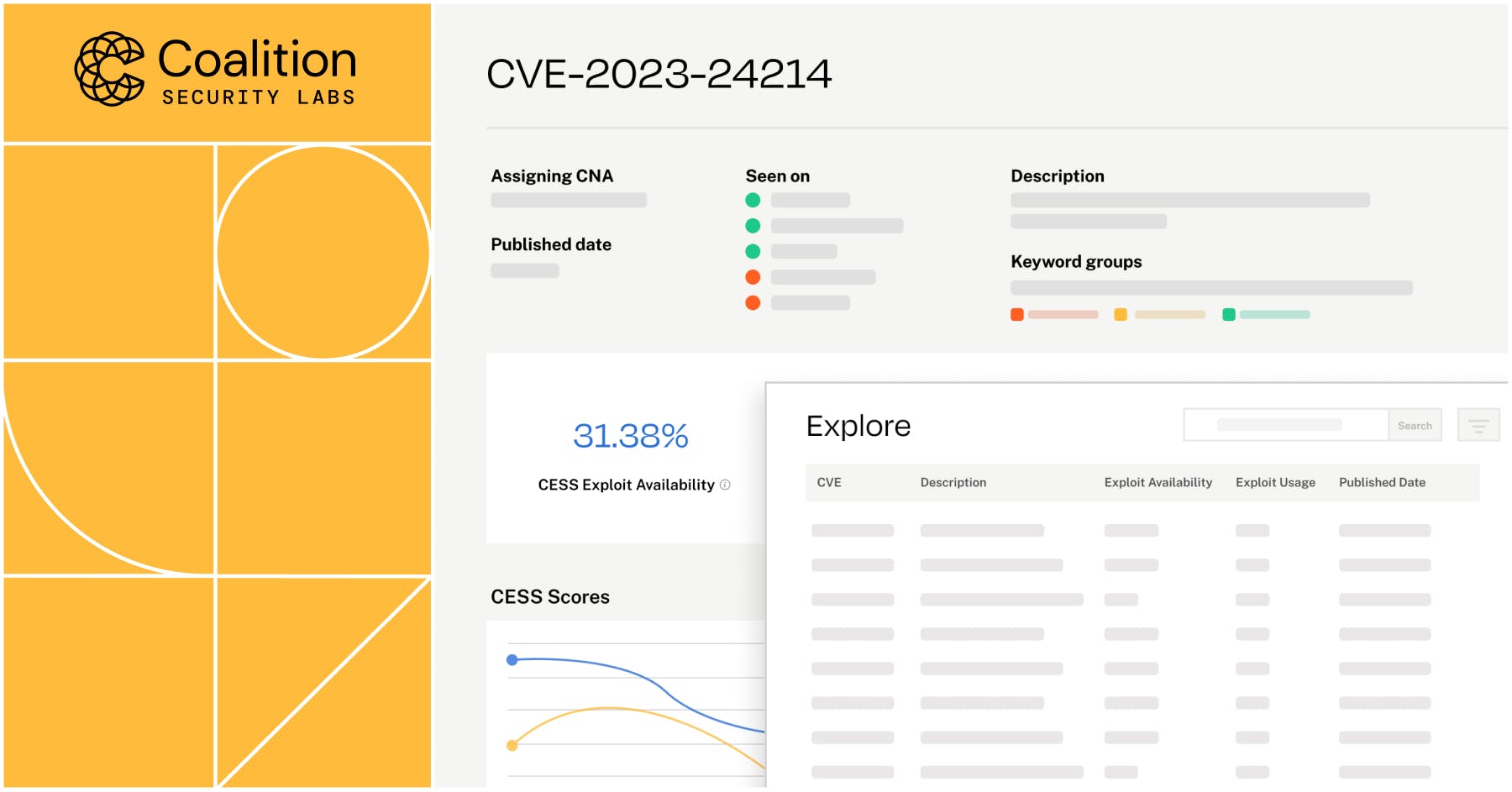
Coalition Exploit Scoring System (Coalition ESS) helps risk managers and defenders cut through the noise surrounding new CVEs by assigning dynamic scores so they can make decisions about patching and mitigation.
Vulnerability management made easy with expedited scoring
Risk managers need to be able to prioritize patching for the new vulnerabilities that are most likely to negatively impact their organization's security posture. Often, the release of a new critical common vulnerabilities and exposures (CVEs) results in an "all hands on deck" situation when, at times, it is over-hyped or altogether unnecessary.
For example, in December 2021, security practitioners rushed to patch the log4j vulnerability (Log4Shell), which saw most exploit attempts peak at 17 days, according to the 2023 Verizon DBIR. In contrast, a critical vulnerability announced by OpenSSL in December 2022 drew significant attention. Teams rushed to patch, expecting a risk on par with Log4Shell, but ultimately OpenSSL had the two CVEs associated with the vulnerability downgraded.
To that end, we developed Coalition ESS as an early source of truth for security risk managers. The Coalition ESS model leverages our proprietary internal data in conjunction with artificial intelligence and large language modeling. The model scans the descriptions used in newly published CVEs and compares them to previously published vulnerabilities to predict the likelihood of exploitability, generating two scores:
Exploit Availability Probability (EAP): the likelihood that an exploit will be made publicly available — which means the code for the exploit is readily available on the internet for threat actors to leverage in their attacks.
Exploit Usage Probability (EUP): the likelihood that threat actors will actually use an exploit to execute a large scale cyber attack.
When a new CVE is announced, risk managers and defenders may turn to the Common Vulnerability Scoring System (CVSS) for severity scores, but industry-standard systems like CVSS take time to score new CVEs.
ESS scores, however, are available the day the vulnerability is announced, unlike CVSS. ESS scores are dynamic, updated as more information becomes available, and with accompanying histories of scores and changes over time. This is a departure from traditional scoring models, which often remain static after issuing.
Prioritize patching with Coalition ESS
Time and workload management are crucial in cybersecurity — the industry is facing a talent shortage, and already overburdened teams may lack resources for tools or services.
With Coalition ESS, IT and security teams have a prioritization list outlining which vulnerabilities pose the greatest threat. This allows defenders to make meaningful decisions about vulnerability management before CVSS scores are available, allocating resources in a timely manner before a vulnerability becomes an emergency.
For example, if a defender notices that a new CVE has a high EAP score and a low EUP score, that tells them that an exploit for the vulnerability exists, even if threat actors have yet to use it actively. From here, they can decide to apply patches or other mitigations and prepare their organization before threat actors utilize the exploit to launch attacks.
Try Coalition ESS today
Coalition ESS is available for public use at ess.coalitioninc.com. We're excited to welcome members of the security community to try Coalition ESS, and we have a robust roadmap for future releases and enhancements to come.
To learn more about Coalition Security Labs' research and innovations, follow us on Twitter @CoalitionSecLab.








