Cyber meltdown and the spectre of uninsurable risk
It’s been an awfully eventful start to the New Year. In case you’ve missed the news, two major security flaws have been discovered in the processors that power nearly all of the world’s computers. The two techniques discovered to exploit these flaws, nicknamed Meltdown and Spectre, could allow hackers to steal data and secrets from any vulnerable computer, including mobile devices. Because the flaws are with the computer processor itself, any software platform running on top of an affected processor is potentially vulnerable.
If by this point you’ve tired of hearing about technology vulnerabilities, this one is different (but also mostly the same, as I’ll get to a bit later). For one, this isn’t a software bug like you might find in your operating system or browser. Nor is it a physical defect in the processor itself. Meltdown and Spectre aren't really "bugs" at all. Instead, they represent methods to take advantage of the normal ways that many processors work for the purpose of extracting secrets and data. More importantly, though, is the magnitude of the impact. By comparison, the WannaCry and NoPetya ransomware attacks wreaked global havoc exploiting vulnerabilities that are believed to have affected ~400,000 computers versus the estimated 2 billion computers susceptible to Meltdown and Spectre.
The timing of these events could hardly come at a more interesting time for the cyber insurance industry. Only a few days prior, in an interview with the Financial Times, Christian Mumenthaler, CEO of Swiss Re, one of the world’s largest reinsurers, questioned the very insurability of cyber risk due to the possibility for accumulation risk — the possibility that a cyber event could hit many insurance policyholders at the same time, by the same attack resulting in huge potential claims payouts.
Sound familiar?
Cut the FUD
In our first blog post (Why we founded Coalition) we observed that we now live at a time where a cyber attack, technology failure, or human error can cause everything from data theft to supply chain disruptions, hospital shutdowns, hotel room lockouts, blackouts, and even nuclear centrifuge explosions—literally the entire spectrum of known risk. That these events could even theoretically occur on a massive scale, and all at once, is certainly cause for alarm—it would indeed pose a serious accumulation risk, and eliminate one of the core pillars of insurability.
However, it would be mistaken to assume that such a scenario, as in the case of Meltdown and Spectre, is anything more than FUD (fear, uncertainty, and doubt). This is hardly to say that the discovery of these security flaws is much ado about nothing. On the contrary, they pose a very real threat, and may well open the door to serious cyber attacks. However, as with the headline-grabbing ransomware attacks of 2017, there are many reasons to believe that subsequent losses will be relatively contained.
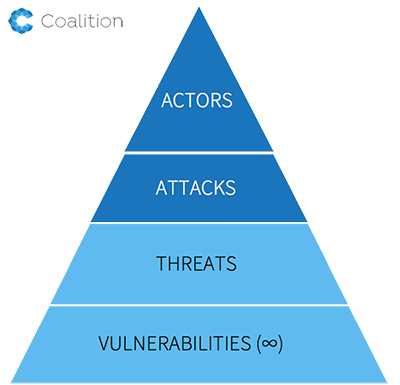
To understand why, it’s helpful to consider the hierarchy of cyber security. At the base are vulnerabilities in all of their forms (software, humans, even processor architectures). That the base is bounded is misleading because, in reality, there are an infinite number of vulnerabilities that can and will exist. However, vulnerabilities only matter if they pose a threat to an organization. This combination of threat and vulnerability is generally the risk an organization faces. Even then, threats don’t matter unless someone proceeds to attack you. And that someone at the top of the pyramid is, 10 out of 10 times, a human actor. Why does this matter?
It matters because cyber attacks are really just forms of cybercrime, which itself is merely a form of crime—it is the people, not the form that matters. There are costs for criminals to launch attacks, and not just the risk of being caught (which for the moment is abysmally low). Criminals require time, infrastructure, and money to fund their enterprises, enumerate targets, and move through the kill chain towards the realization of their desired outcomes. All the while they must also factor in the uncertainty of achieving this outcome.
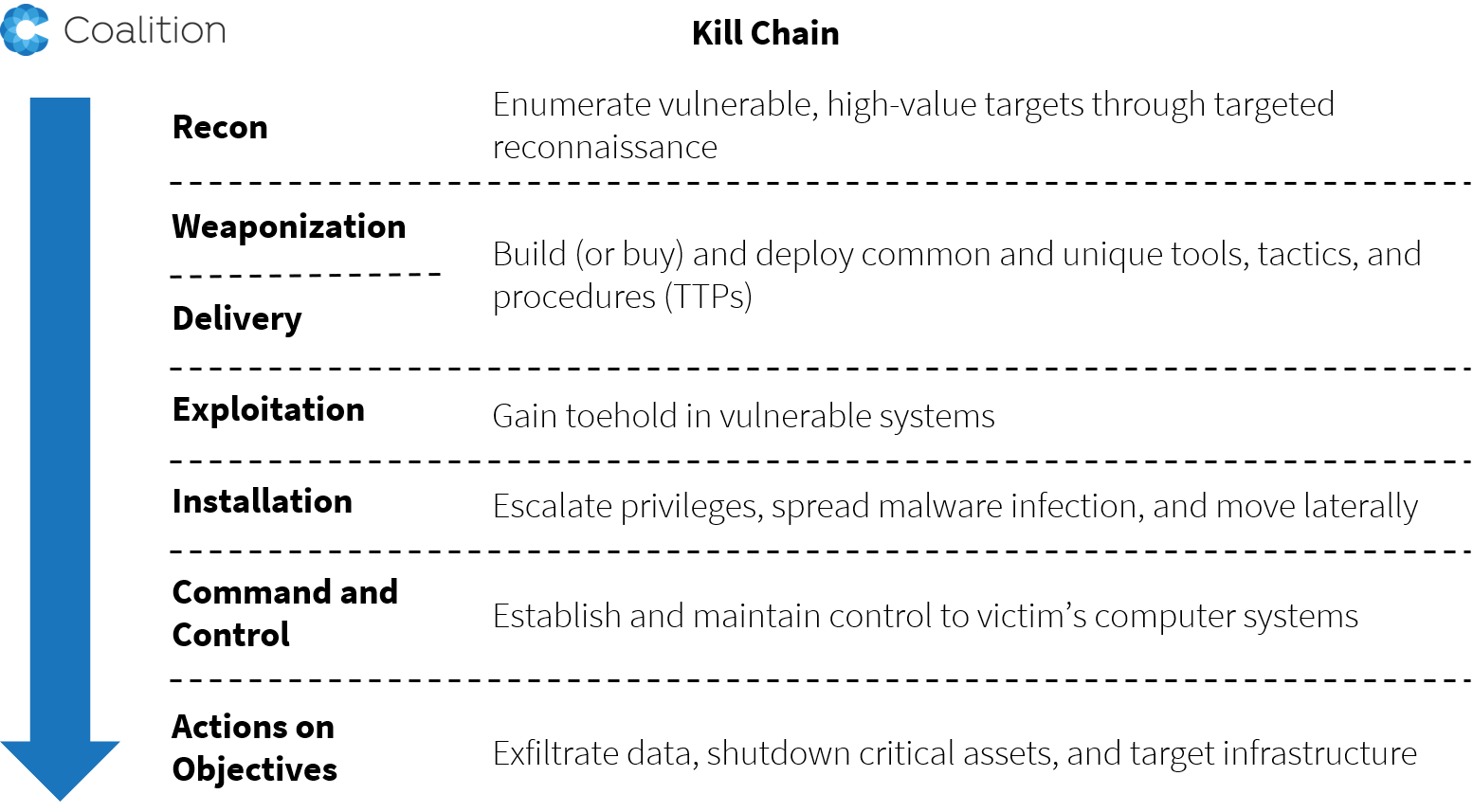
Exploits for security flaws can accomplish many things, but few output cash. Every step in this chain takes effort. Although cyber criminals are becoming more numerous and sophisticated, they are still limited in how much damage they can cause, and profit they can reap. As a result, even though an *entire* population may be vulnerable, the economically optimal strategy for an attacker is nonetheless to focus on a relatively small set of victims.
Cyber insurance is dead. Long live cyber insurance!
Although there is little doubt that certain accumulation scenarios exist limiting the insurability of certain cyber risk exposures, this is not one of them. Absent an expertise in hacking and cybercrime—and the economics thereof—it is no surprise that many insurers offering cyber insurance struggle to understand, much less manage, accumulation risk. It’s high time they woke up.
We believe insurance to be the primary tool to solve cyber risk. This means that insurers must come to realize the role that insurance plays in protecting companies from all forms of cyber risk. It also means thinking about cyber insurance as more than just coverage for data breach and response. The most recent devastating attacks have resulted in business and supply chain interruption, and even physical property damage. It is hardly a stretch to imagine exposure to nearly every other form of known risk, including bodily injury or even pollution. Of course, with new exposures come new challenges in underwriting and management of accumulation.
This is why we at Coalition seek to help define and lead the next generation of cyber insurance. Of course, doing so won’t be easy. It will mean using data in an entirely novel way to not only assess the risk of an individual policyholder, but an entire population of policyholders, and doing so on a continuous basis.
It will also mean measuring diversity, and particularly technological diversity, to manage accumulation in novel ways. How many insurers today know which cloud service provider their clients use, much less which versions of software they are running? Or whether their clients’ passwords have been compromised in a third-party data breach? If you don’t know these answers, you’re in trouble. Gone are the days when accumulation will be managed by geography, industry, and revenue size. Fortunately, we’re up to the challenge.
Long live cyber insurance.







