July Risk Roundup: Cloudy with a chance of outdated equipment

Everyone enjoys the opportunity to be creative, and there’s no reason managing your IT environment can’t be as creative as that Tweet you’ve spent all morning crafting. Staying on top of your systems, be it patching, upgrades, or ensuring proper management of your cloud infrastructure (while avoiding shadow IT) should be fun — and a little creative.
1. Hubble, Hubble, toil and trouble
Old, outdated, unsupported equipment is a security risk; availability is a core security concern. Attackers can exploit vulnerabilities, and repairing or replacing old systems may be impossible (though most of us can get to our systems a little easier).

2. Protecting your business against malware in the cloud
Important reminder: cloud computing is not a set-it-and-forget-it solution. Tripwire has shared some excellent advice to get you started. Just remember that security in the cloud follows a shared responsibility model, meaning you still have some work to do. Your cloud provider is not responsible for your security.

3. Infosec limerick contest
First sea shanties and now limericks? Fighting burnout in cybersecurity is a full-time job, so we say have some fun — do haikus next.
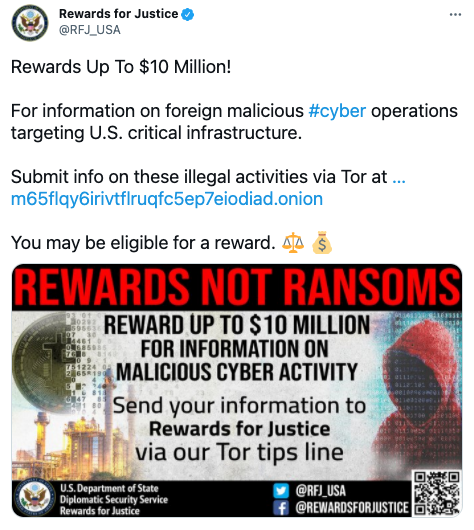
4. Rewards up to $10 million
$10 million for reporting ransomware, and the reporting mechanism is set up on a Tor site to preserve security and anonymity of the reporters? Not a hot take so much as kudos to the State Department in helping fight ransomware.
View tweet here If you enjoyed this post be sure to check our blog weekly; the Risk Roundup runs Friday mornings in addition to more enlightening content we post related to the ever-evolving landscape of digital risk. Follow us on Twitter (@SolveCyberRisk) and LinkedIn (Coalition Inc). If you have any suggestions for content that we should be adding to our reading list, let us know!







